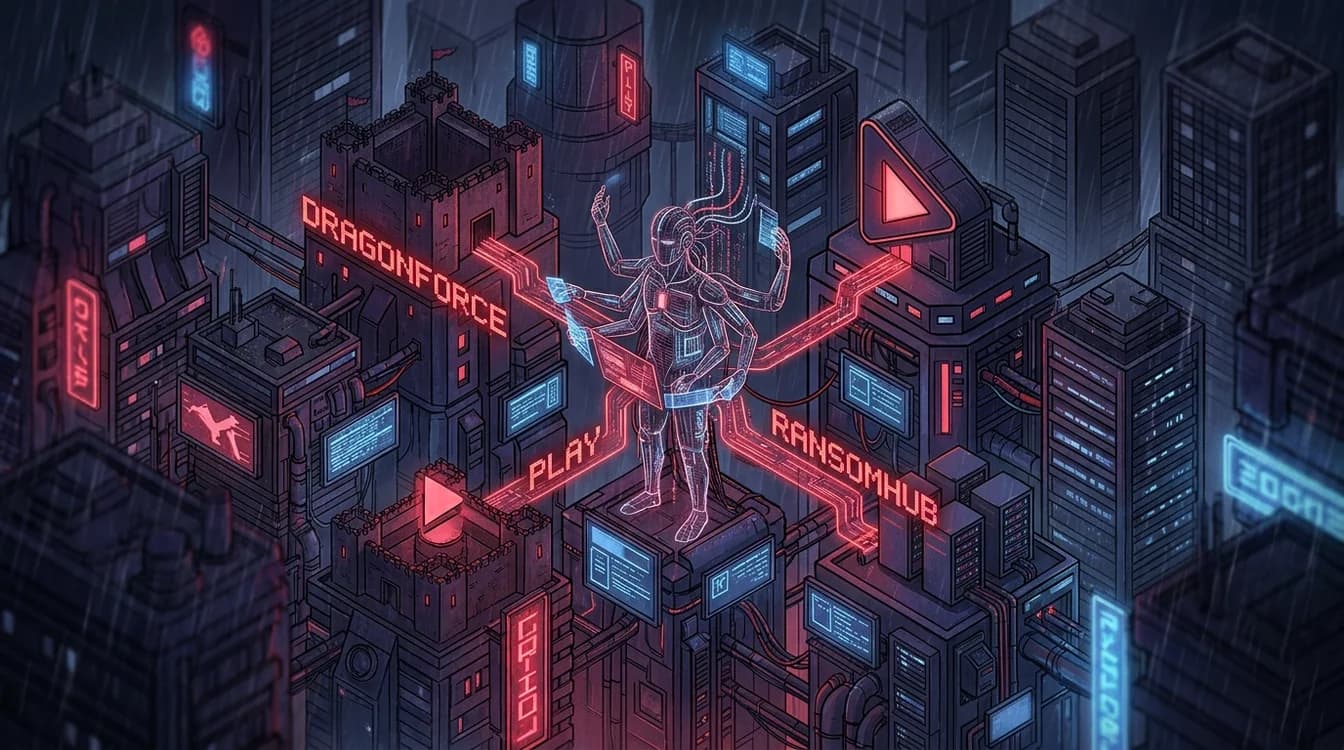
Scattered Spider: Identity-First Attack Chain
Investigate a high-sophistication intrusion by UNC3944 (Scattered Spider). This scenario simulates a multi-stage attack starting from social engineering and MFA fatigue, progressing through the exploitation of unmanaged edge devices, and culminating in a 'Bring Your Own Vulnerable Driver' (BYOVD) technique to blind kernel-level security agents. Analysts must correlate identity providers, cloud sign-ins, and deep endpoint forensics to reconstruct the timeline and identify the breakout speed of this financially motivated threat actor.