Bumblebee to Akira: Search Engine Poisoning Pipeline
Investigate a high-stakes 2025 intrusion where a simple search engine result led to a full-scale Akira ransomware deployment. This scenario tracks the transition from initial access via Bumblebee to post-exploitation via AdaptixC2, culminating in domain-wide encryption. You will analyze the browser-to-endpoint execution chain, identify lateral movement via administrative tools, and uncover the specific techniques used by the Howling Scorpius group to evade modern EDR solutions.
Start this operation
Create your free account and begin immediately.
Get Early Access — FreeFree forever — no credit card required
Investigation Tasks
Complete each task by investigating alerts and submitting your findings.
Investigating Suspicious DLL Execution on corp-wks-112
12On 2025-08-01T13:41:59.733Z, an alert was triggered on corp-wks-112 involving an unusual execution pattern by amanda.garcia. You must identify the malicious payload's signature that was passed to the system process to determine the extent of the compromise.
Identify the Malicious Payload Execution
6An alert was triggered when an unusual child process was spawned by the Windows shell. Investigate the execution chain starting from explorer.exe to find the external payload that was downloaded and executed by the attacker.
Investigating Suspicious File Activity on corp-wks-442
6During the investigation into a possible C2 callback to domain1.com, a PowerShell process was observed executing on amanda.garcia's workstation. Analyze the xdrContent to determine the name of the file that was targeted or created during this specific event.
Identifying Malicious C2 Infrastructure
2After an alert for suspicious network activity on corp-wks-442, we need to identify the command-and-control infrastructure. Examine the XDR timeline events to find the specific domain the system attempted to contact during the initial beaconing phase.
Investigating Initial Payload Delivery
6An alert was triggered regarding suspicious network activity involving powershell.exe on workstation corp-wks-442. Analyze the XDR Timeline to determine what specific external image file was mounted or accessed during the initial stage of the compromise at 2025-08-01T10:17:57.218Z.
Investigating Suspicious DLL Execution on corp-wks-112
12At 2025-08-05T11:29:59.319Z, an unusual process execution was flagged on corp-wks-112 involving the user robert.chen. You must investigate the logs to determine the unique file hash associated with this execution to confirm if it matches known C2 infrastructure patterns.
Identifying Anomalous Execution Patterns
6A suspicious connection to domain1.com was detected originating from a workstation assigned to amanda.garcia. You must correlate this network activity with the endpoint events to determine which non-standard process initiated the sequence of events during the compromise.
Identifying Compromised Administrative Accounts
2During a routine audit, an alert was triggered involving rundll32.exe and powershell.exe communicating with domain1.com. You need to investigate the XDR process data to determine which user account was used to initiate these suspicious activities.
8 tasks · 52 points total
Start investigationTraining Tools
Skills You'll Build
Requires foundational alert triage skills. Multiple data sources to correlate.
Prerequisites
- Basic understanding of security alerts
- Familiarity with SIEM concepts
- Familiarity with XDR concepts
Ready to investigate?
Create your free account and begin immediately.
Get Early Access — FreeFree forever — no credit card required
More Operations
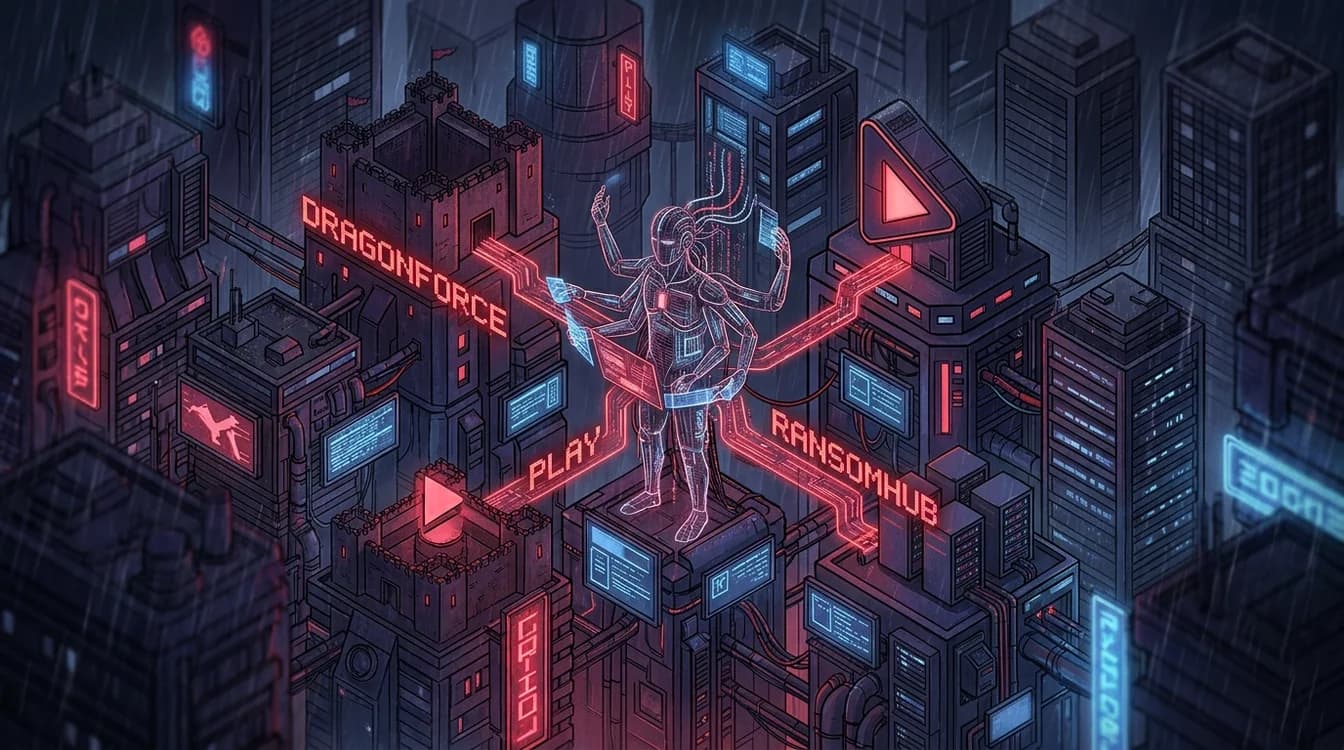
View allScattered Spider: Identity-First Attack Chain
Investigate a high-sophistication intrusion by UNC3944 (Scattered Spider). This scenario simulates a multi-stage attack starting from social engineering and MFA fatigue, progressing through the exploitation of unmanaged edge devices, and culminating in a 'Bring Your Own Vulnerable Driver' (BYOVD) technique to blind kernel-level security agents. Analysts must correlate identity providers, cloud sign-ins, and deep endpoint forensics to reconstruct the timeline and identify the breakout speed of this financially motivated threat actor.
Fake Zoom to Ransomware: The Social Engineering Pipeline
In this advanced SOC simulation, you will investigate a multi-stage intrusion that began with a drive-by download of a trojanized Zoom installer. The attack progressed through several stages of loader execution, including d3f@ckloader and IDAT loader, eventually leading to the deployment of high-end C2 frameworks like Cobalt Strike and Brute Ratel. You must trace the attacker's path from the initial web-based compromise, through lateral movement via RDP tunneling and proxy tools, to the final mass-deployment of BlackSuit ransomware via enterprise management software. This scenario is based on real-world 2025 threat intelligence and requires deep analysis of SIEM, XDR, and Firewall telemetry to reconstruct the full kill chain.
Black Basta: Email Bomb to Encryption
Investigate a sophisticated Ransomware-as-a-Service (RaaS) campaign involving Black Basta and Cactus TTPs. This scenario tracks a multi-stage attack from initial social engineering via Microsoft Teams and Quick Assist to advanced persistence using DLL side-loading in OneDrive. You will analyze how attackers move from identity-based initial access to full domain compromise and ESXi virtualization host encryption. The investigation requires correlating evidence across SIEM logs, XDR process trees, and firewall traffic to uncover hidden C2 channels and data exfiltration patterns occurring during off-hours.